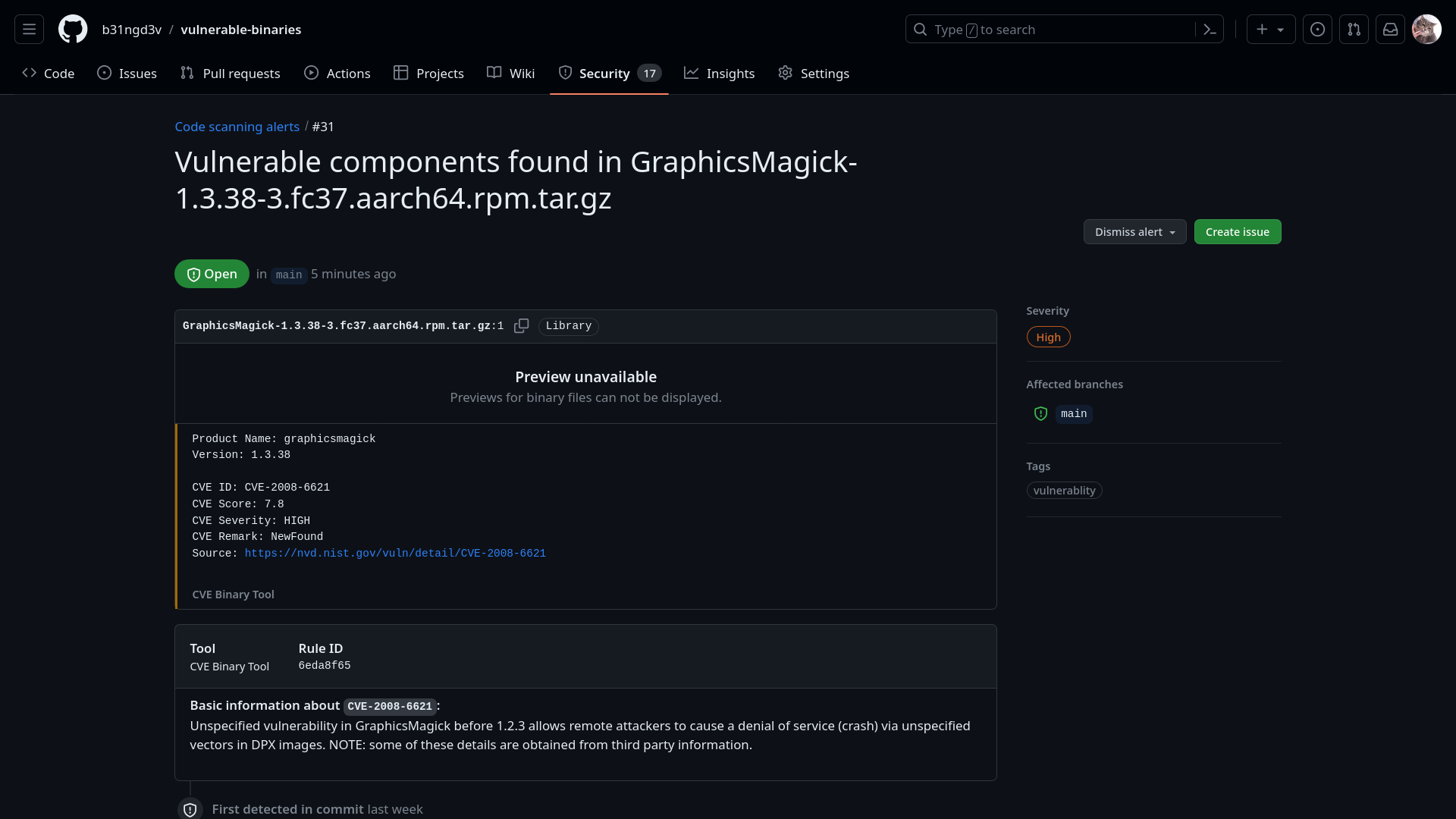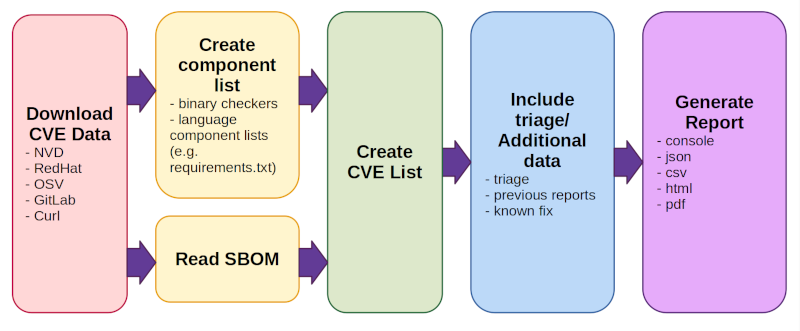
GitHub - intel/cve-bin-tool: The CVE Binary Tool helps you determine if your system includes known vulnerabilities. You can scan binaries for over 200 common, vulnerable components (openssl, libpng, libxml2, expat and others),
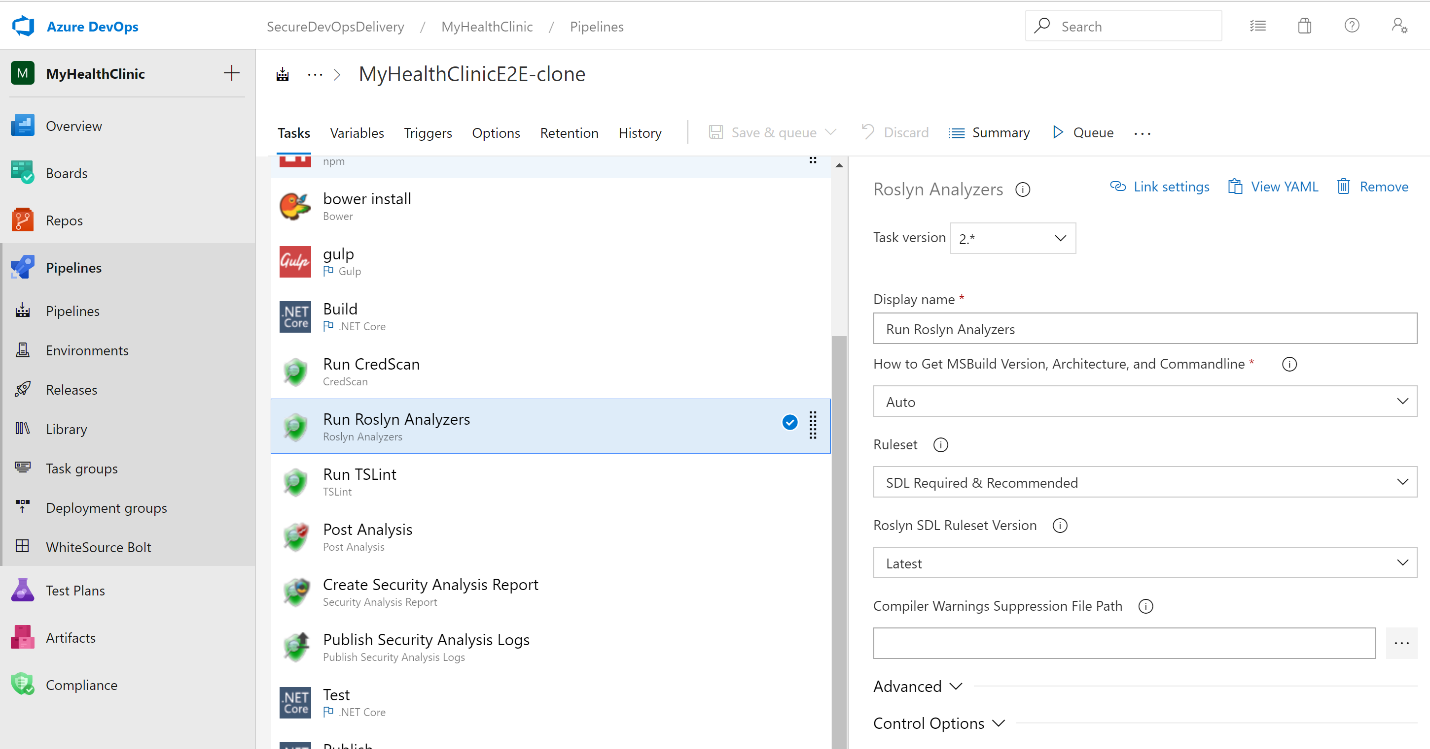
Microsoft Security Code Analysis – a tool that seamlessly empowers customers to enable security controls in your CI/CD pipeline - Developer Support
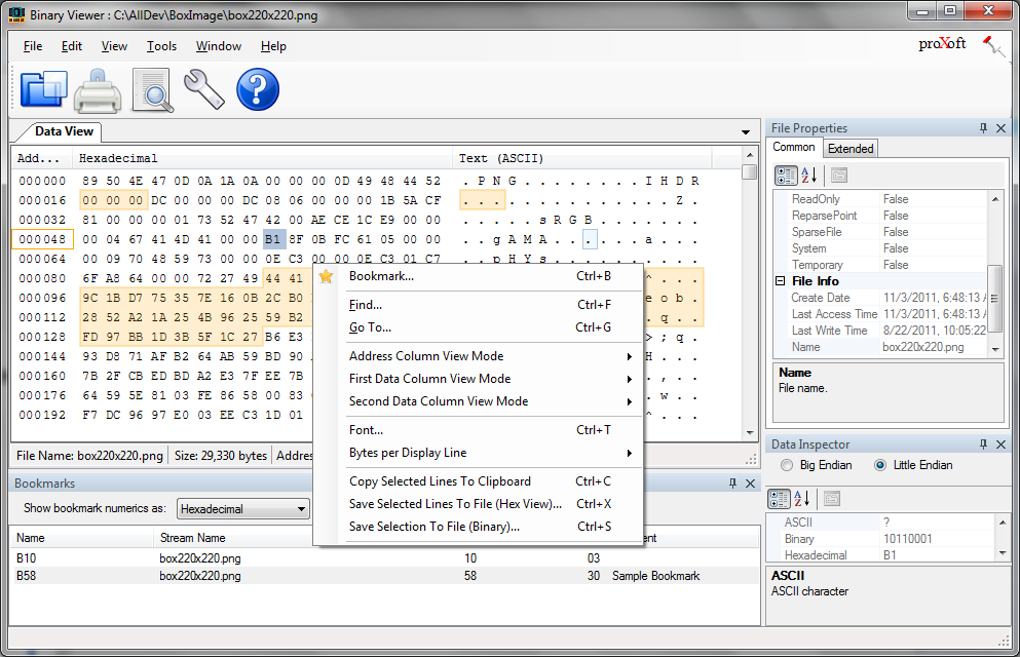
GitHub - starfleetcadet75/binaryninja-yara: YARA signature scanner for Binary Ninja with built-in cryptographic signatures
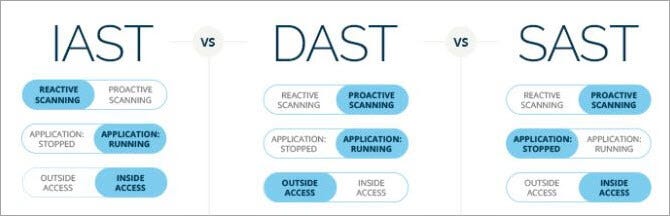
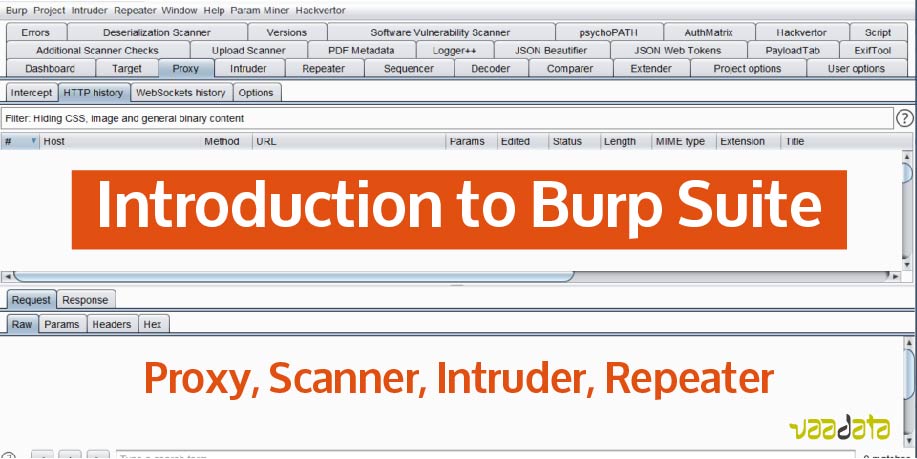
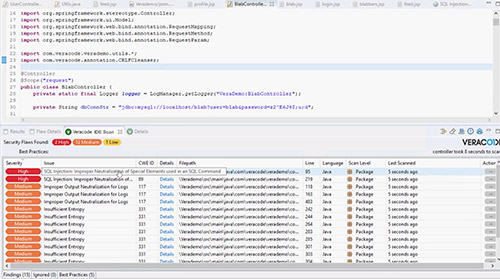
Ensuring Robust Application Security: Exploring SAST, DAST, and IAST for Comprehensive Protection | by Ranjan Singh | Medium
How does static binary analysis work? What type of internal modeling is performed (e.g., dataflow, controlflow, etc.)