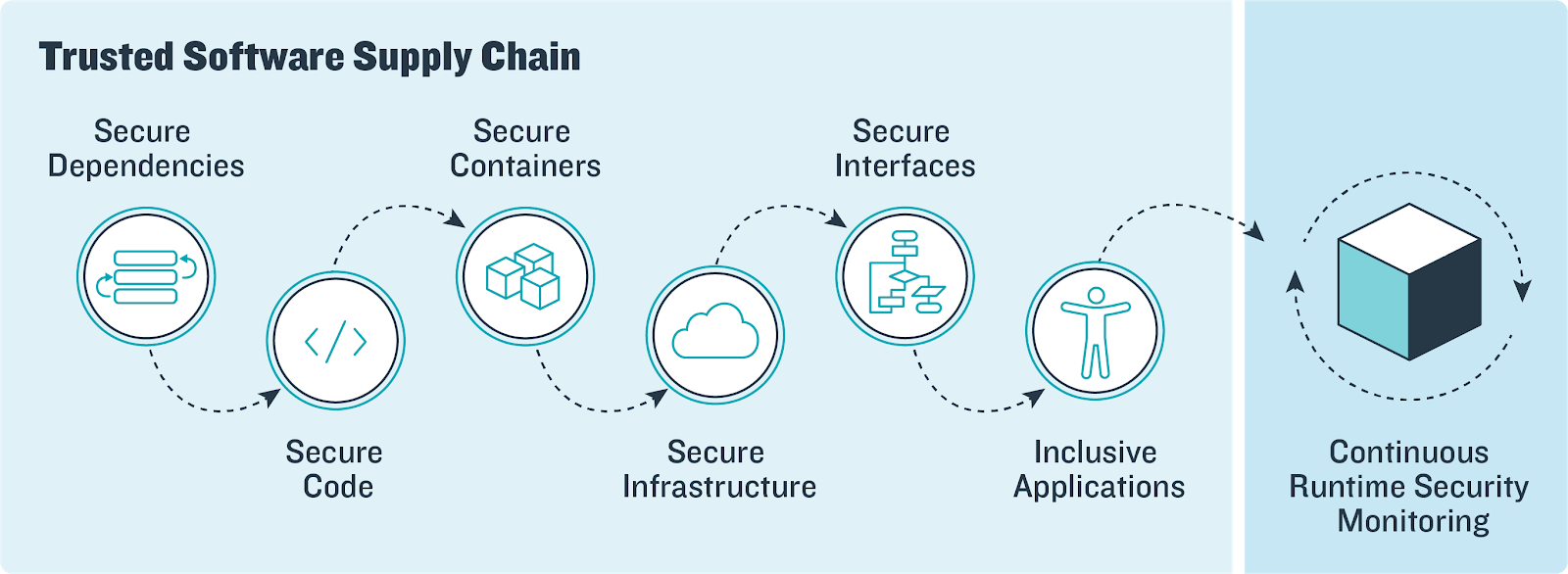
How Software Supply Chain Attacks Work, and How to Assess Your Software Supply Chain Security | Mend.io
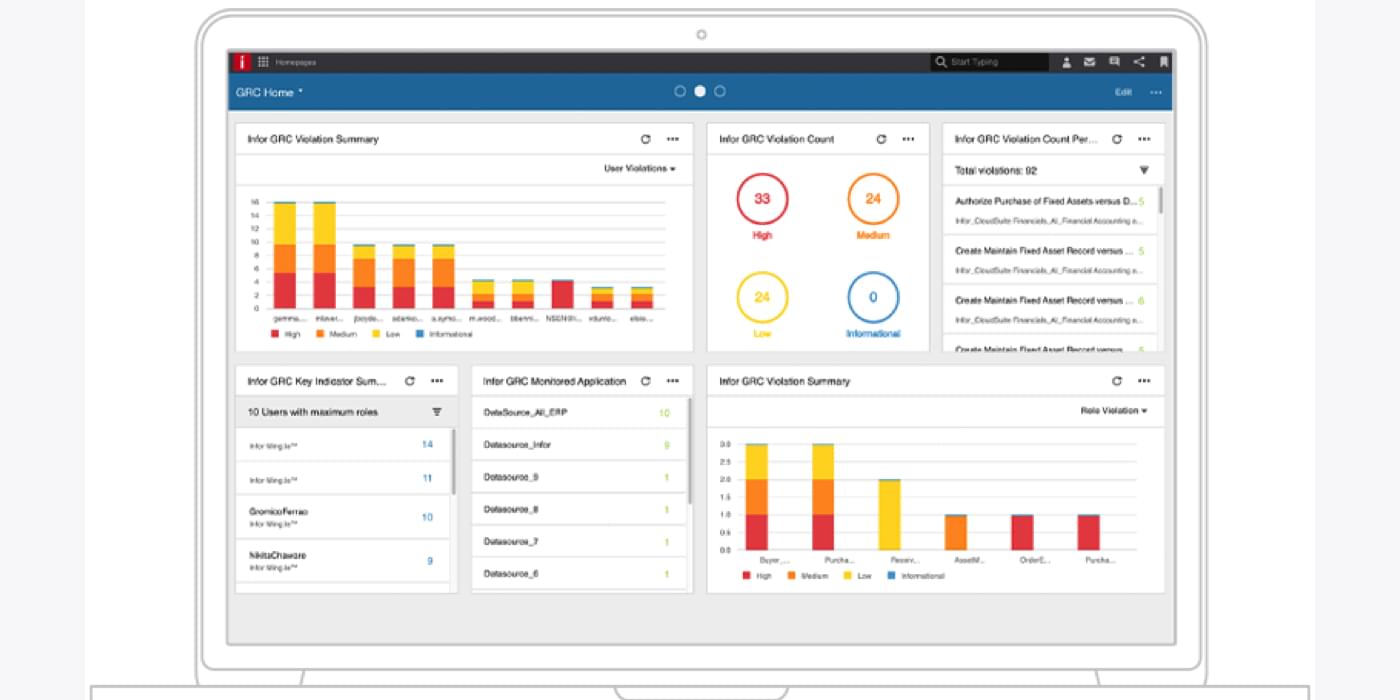
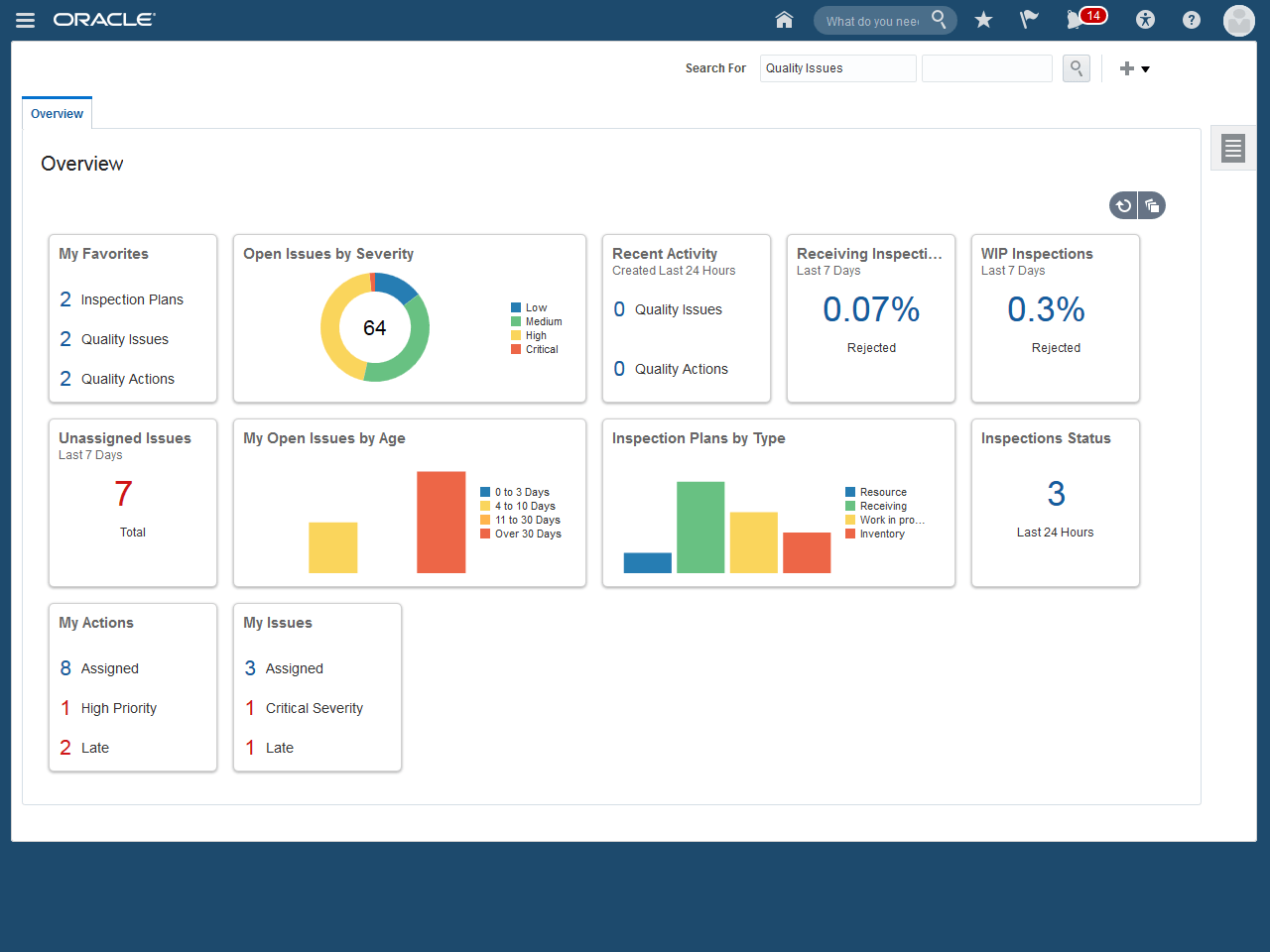
Top 13 Supply Chain Analytics Software in 2024 - Reviews, Features, Pricing, Comparison - PAT RESEARCH: B2B Reviews, Buying Guides & Best Practices