How to exploit the VMware vCenter RCE with Pentest-Tools.com (CVE-2021-21985) | Pentest-Tools.com Blog
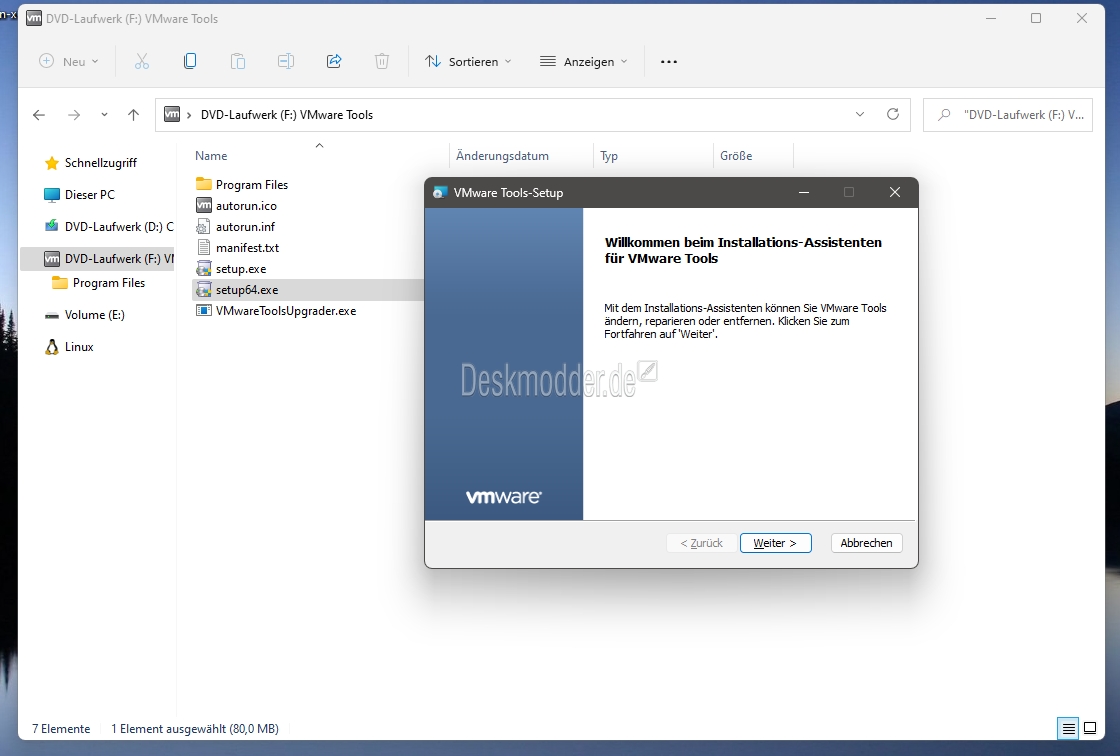
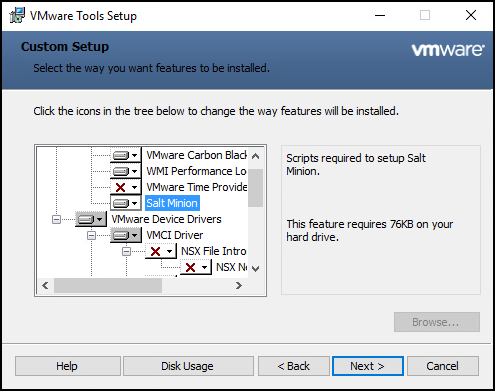
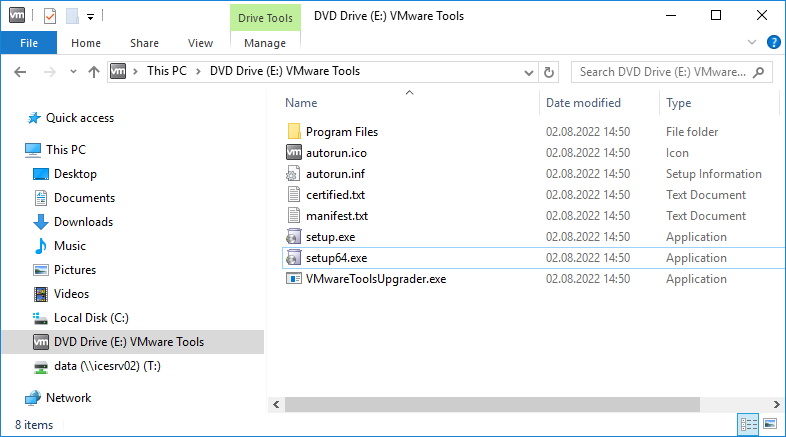
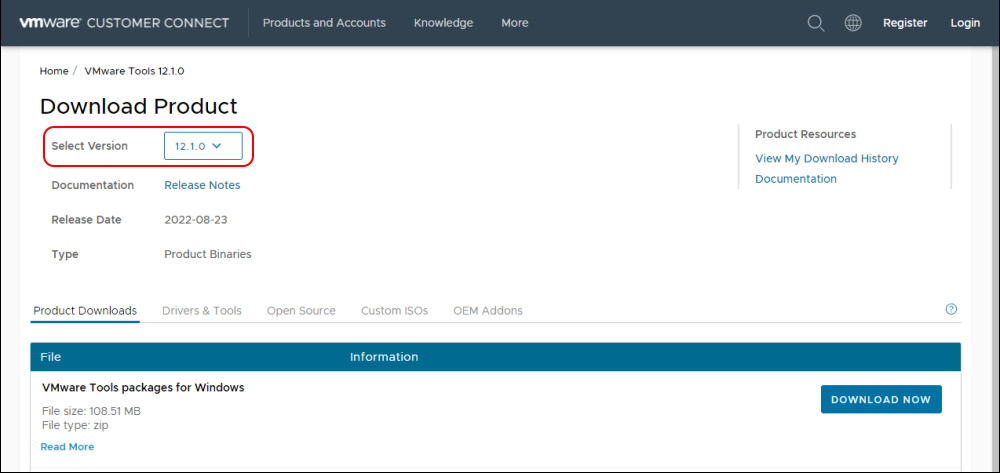
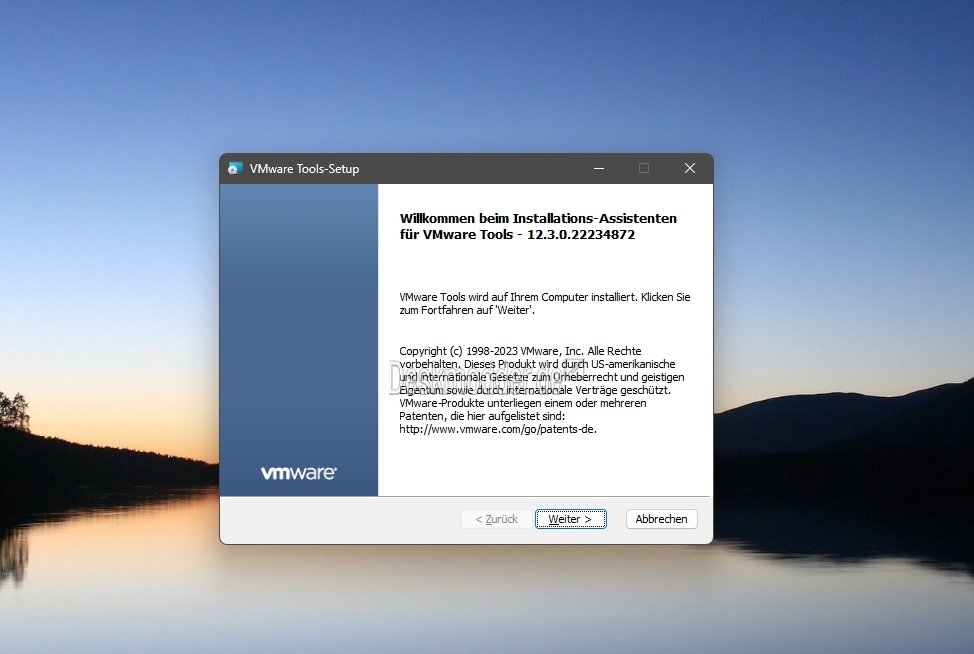
VMWare Tools 12.0.0 korrigiert eine Sicherheitslücke und unterstützt offiziell Windows 11 und Server 2022 - Deskmodder.de

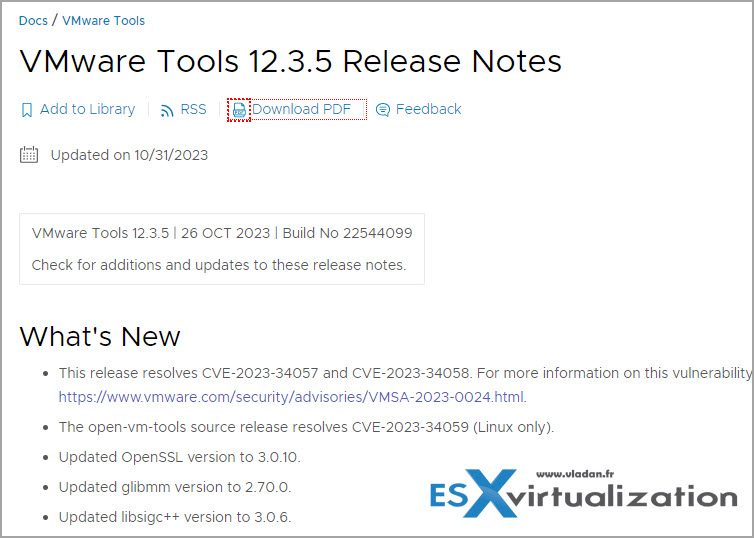
High-Severity VMware Tools and vCenter Server Vulnerabilities Addressed with Recent Patches (CVE-2023-34057, CVE-2023-34058, CVE-2023-34048)
![VMware Tools out of bounds read vulnerability [CVE-2019-5522 and CVE-2019-5525] - SystemTek - Technology news and information VMware Tools out of bounds read vulnerability [CVE-2019-5522 and CVE-2019-5525] - SystemTek - Technology news and information](https://i0.wp.com/systemtek.co.uk/wp-content/uploads/2018/10/vmware-390x205.jpg?fit=390%2C205&ssl=1)
VMware Tools out of bounds read vulnerability [CVE-2019-5522 and CVE-2019-5525] - SystemTek - Technology news and information

High-Severity VMware Tools and vCenter Server Vulnerabilities Addressed with Recent Patches (CVE-2023-34057, CVE-2023-34058, CVE-2023-34048)

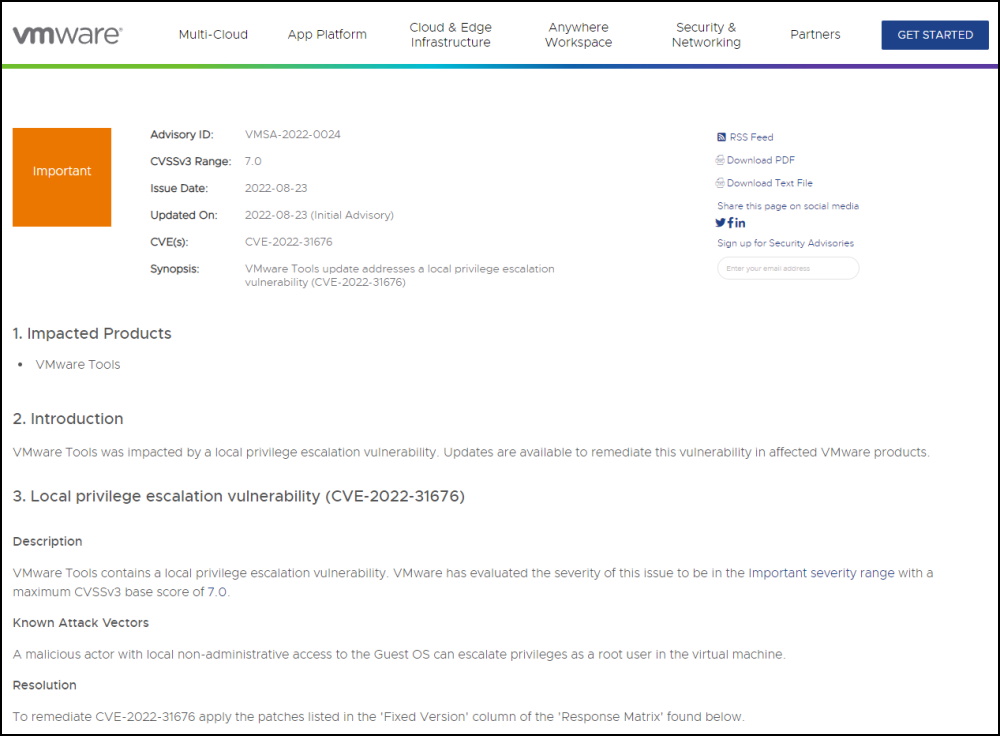
VMware Tools update addresses a local privilege escalation vulnerability ( CVE-2022-31676) with a maximum CVSSv3 base score of 7.0 : r/cybersecurity
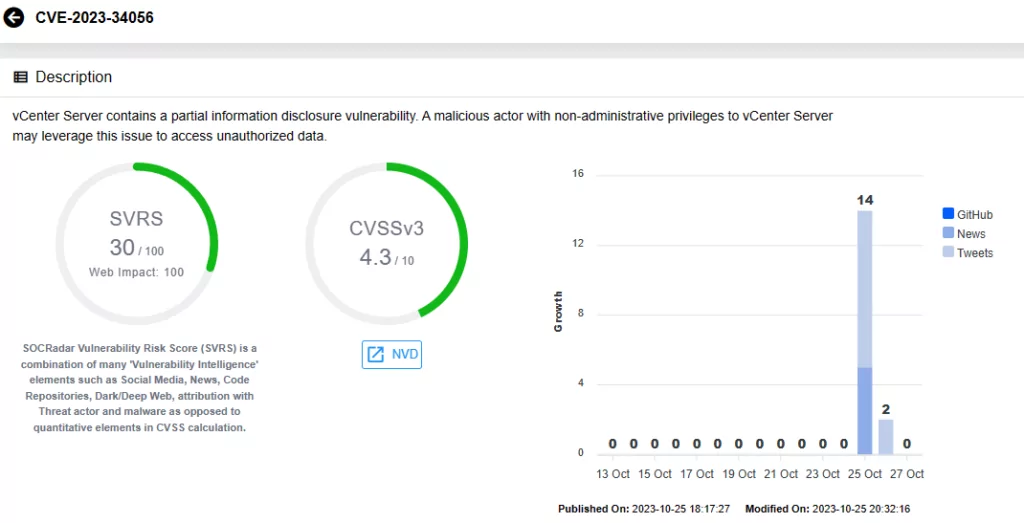
High-Severity VMware Tools and vCenter Server Vulnerabilities Addressed with Recent Patches (CVE-2023-34057, CVE-2023-34058, CVE-2023-34048)